From time to time, technical improvements to the FrontStream Payment Gateway will require a more in-depth discussion. The pages below provide best practices, FAQ, and up-to-the-minute information related to each improvement.
If you don’t understand a term in this section, it means the testing doesn’t apply to you. For example, if you don’t know if you have an API, ignore that section. People who do have an API know it.
To test your browser, just open your browser and go to this site: https://www.howsmyssl.com/
If you do see “Probably Okay”, that’s the highest grade and means you’re using TLS 1.2, so your browser does not have a TLS 1.0 issue.
If you don’t see “Probably Okay”, just upgrade your browser to the highest version available and test again. In the rare cases where you still don’t get “Probably Okay”, talk to your computer support people. You might need a newer computer.
To test the protocols supported on a website, run this link configured for whatever site you want to test:
https://www.ssllabs.com/ssltest/analyze.html?d=mywebsite.com
e.g.
https://www.ssllabs.com/ssltest/analyze.html?d=test.ftipgw.com
If you have your own API that others call, you can test the API using SoapUI (a professional testing tool requiring some developer skills).
If your code calls someone else’s API, your best bet is to work with the API vendor.
Dear Client:
We take the security of your information seriously, and we want to let you know about upcoming data encryption changes that may impact you.
In the 2nd quarter 2018, we are ending our support of the RC4 encryption cipher and the TLS 1.0 encryption protocol. We are reminding all clients to make sure their web browsers and payment processing solutions are updated before the 2nd quarter.
An encryption cipher is required for any transaction, whether it’s processed using a terminal, website or an app. RC4 is just one of many encryption ciphers that your point-of-sale solution might be using, and it no longer meets Payment Card Industry security standards. If your solution is using only this one cipher, then your payment processing will be interrupted in the 2nd quarter.
An encryption protocol is required for any transaction, whether it’s processed using a terminal, website or an app. TLS 1.0 is just one of many encryption protocols that your browser or payment software might be using, and it no longer meets Payment Card Industry security standards. If your solution is using only this one protocol, then your payment processing will be interrupted in the 2nd quarter.
If you have questions or concerns,
We appreciate your business. Thank you for choosing FrontStream.
A: On this page.
BrowserTestBrowserTest9 
Your reseller/vendor/integrator will contact you about whether you need to test, and if so, how to test, but here is the general idea: Pick any time from 1:30 PM Pacific (4:30 PM Eastern) through the night until 6:30 AM Pacific (9:30 AM Eastern) the next day. Tests run outside this 17-hour window are invalid. Any time is OK for testing except 6:30 AM – 1:30 PM Pacific.
PartnerID/Reseller: 100
Vendor/Merchant/RPNum/MerchantKey: 715
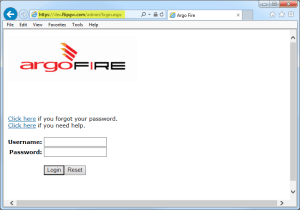
Username: fpwz6932
Password: QNn9Yrjt
URL: dev.ftipgw.com (not secure.ftipgw.com)
Name on Card: RC4 Test – <something to identify the device you ran from >,
e.g. RC4 Test – Cashier 1
Visa Test Card Number: 4055 0167 2787 0315
CVV: 123
Expiration: 12/19
Amount: $5.00
(If the following applies to you, you’ll understand what it means.) If the software you are testing uses a PNRef as a token for a stored credit card number, and then runs subsequent charges using that token, PNRef 565492 is an Approved transaction against the above Visa/Expiration/Amount, so use 565492 if you need a PNRef for your testing.
The cipher/protocol set toggles on the test server at dev.ftipgw.com. For a 6-hour window, TLS 1.0 is enabled. For a 17-hour window, TLS 1.0 is disabled. However, 24 hours a day, RC4 cipher is disabled and TLS 1.2 is enabled.
InformationWeek
How the RC4 cipher is vulnerable
PCI council changed the official date to June 2018 from June 2016 but there’s a big security risk and Frontstream will be closing the risk by 1st Quarter 2016 and will be disabling TLS1.0 and only supporting TLS1.2 and above regardless of the council’s plan to extend the window for companies who complained that it would take a lot of time to upgrade their systems and services.
http://blog.pcisecuritystandards.org/pci-changes-date-for-migrating-from-ssl-and-early-tls http://blog.pcisecuritystandards.org/impact-new-migration-dates-ssl-early-tls https://www.pcisecuritystandards.org/documents/Migrating_from_SSL_Early_TLS_Information%20Supplement_v1.pdf
Copyright 2025 FrontStream Holdings, LLC.
FrontStream Payments is a registered ISO/MSP of Elavon, Inc, Georgia, First National Bank of Omaha, Omaha, NE, Citizen Bank N.A.,
Providence, RI, and Wells Fargo Bank, N.A., Concord, CA., Peoples Trust Company, Vancouver, Canada